NIS vs NIS2 Directive: Every Key Difference Listed
Key Takeaways on NIS vs NIS2 DifferencesNIS2 significantly ...

Author:
Tomislav Horvat
A NIS2 gap analysis helps identify compliance shortfalls and protects your organization from potential fines up to €10 million or 2% of global turnover, while also strengthening your security posture.
Determine if your organization falls under NIS2 scope based on size thresholds and sectors, then assemble a cross-functional team including IT security, legal, risk management, and business unit representatives.
Systematically assess your current security controls against NIS2 requirements, documenting gaps and prioritizing them based on risk exposure, implementation complexity, and available resources.
Develop a comprehensive remediation roadmap with clear responsibilities, realistic timelines, and measurable milestones, keeping in mind compliance checks begin in 2026.
Implement continuous monitoring mechanisms and maintain thorough documentation of all compliance activities, preparing audit-ready packages that demonstrate your ongoing commitment to NIS2 requirements.
Think of a NIS2 gap analysis as a health check for your organization's cybersecurity measures.
It helps you spot the differences between what you're currently doing and what the NIS2 Directive requires.
Time is running out to start the NIS2 compliance process.
While compliance checks are expected to begin in 2026 (depending on Member State implementation), preparing your systems and processes takes significant time and planning.
The stakes are pretty high too. If you don't comply, your organization could face serious penalties.
Essential entities might see fines up to €10 million or 2% of global turnover, while important entities could face fines up to €7 million or 1.4% of turnover.
What makes this particularly concerning for many organizations is the personal liability angle.
Senior managers and board members could face personal fines or even criminal penalties for non-compliance.
In some cases, you might even be temporarily banned from your management role if serious breaches occur.
Beyond avoiding penalties, this analysis helps strengthen your defenses against cyber threats that seem to grow more sophisticated by the day.
Let's cut to the chase – NIS2 casts a much wider net than its predecessor, and you need to know if you're caught in it.
NIS2 applies to organizations in two main categories: "essential entities" and "important entities."
The directive specifically covers medium and large enterprises in designated sectors, using clear size thresholds:
Medium-sized entities: organizations with 50-249 employees and annual turnover exceeding €10 million or balance sheet over €10 million
Large entities: organizations with 250+ employees or annual turnover exceeding €50 million or balance sheet over €43 million
If you're in these sectors as an essential entity, NIS2 applies to you:
Energy (electricity, oil, gas, district heating/cooling)
Transport (air, rail, water, road)
Banking and financial market infrastructure
Health (including healthcare providers, labs, pharma manufacturing)
Drinking water and wastewater
Digital infrastructure (internet exchange points, DNS providers, TLD registries, cloud services, data centers, content delivery networks, trust services)
Public administration (central and regional government)
Space
Important entities include businesses in:
Postal and courier services
Waste management
Chemicals manufacturing
Food production
Manufacturing (medical devices, electronics, machinery, vehicles)
Digital providers (online marketplaces, search engines, social networks)
The directive also includes specific exemptions.
For instance, entities in defense, national security, public security, law enforcement, judiciary, parliaments, and central banks are typically excluded from scope.
If you're uncertain about your status, consult with legal experts familiar with NIS2 implementation in your specific EU member state, as there may be slight variations in national implementations.
You can't tackle NIS2 compliance from a single department.
You'll need a diverse team that brings different perspectives to the table.
Start with the obvious players – IT security experts who understand the technical requirements and legal/compliance folks who know the regulatory landscape.
But don't stop there.
Pull in representatives from key business units that will be affected by the changes.
Risk management should definitely have a seat at the table too.
Senior management involvement is crucial since they need to understand what's at stake and have the authority to green-light resources and decisions.
Sometimes, an outside perspective helps, so consider bringing in consultants with NIS2 expertise if your in-house knowledge has gaps.
Remember to designate someone as the project lead – the person who'll keep everyone moving in the same direction.
And be realistic about time commitments.
Your team members need enough bandwidth to give this project the attention it deserves.
This isn't something they can squeeze in between their regular responsibilities.
Before jumping into the analysis, take time to map out what success looks like.
What exactly are you trying to achieve?
Your goals should connect with your broader compliance strategy and business objectives.
Create measurable targets for your gap analysis – maybe it's assessing a certain percentage of requirements or reaching a specific level of detail in your findings.
And be mindful of timing.
With compliance checks expected to begin in 2026, your timeline needs to be realistic but should acknowledge that thorough preparation takes time.
Be crystal clear about what falls within your assessment scope.
Which systems, processes, and data will you evaluate?
What will the final outputs look like? Think about documentation formats, reporting structures, and action plan templates.
One last thing – make sure your executive team is on board and ready to commit resources.
Without leadership backing, you might find yourself short on time, people, or budget to complete the process properly.

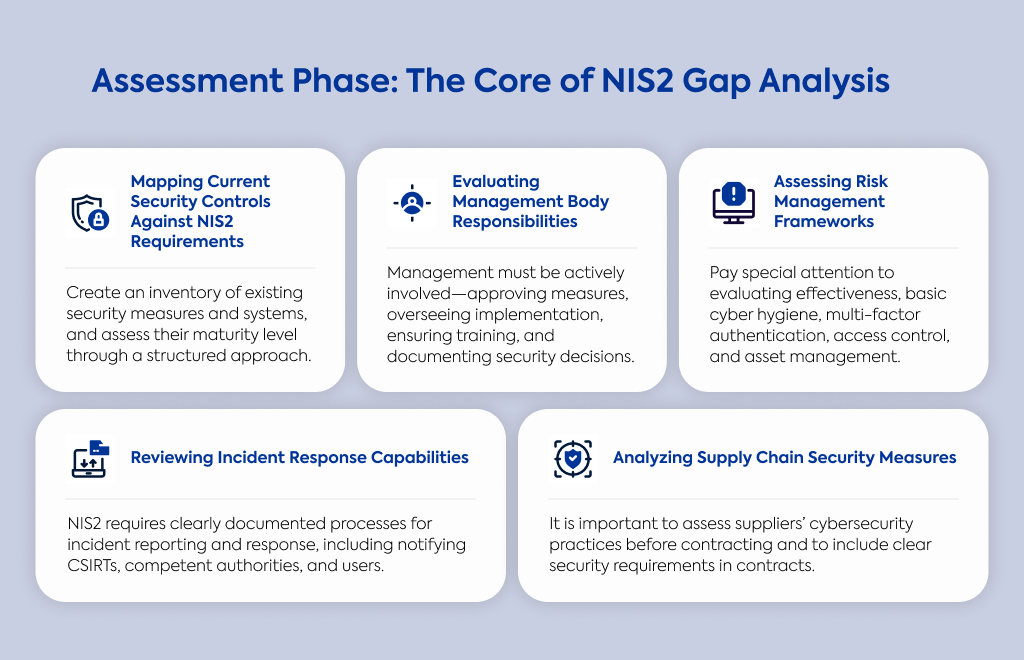
Time to roll up your sleeves and take stock of your current security measures.
Start by documenting what you already have in place and create a complete inventory of all network and information systems within scope.
A structured approach helps here.
Many organizations use a simple rating system – something like a 5-point scale from "Not implemented" to "Optimized" – to assess their current state against each requirement.
This gives you a clear visual of where you stand.
Go through all your existing documentation – security policies, incident response plans, risk assessments, the works.
Look at certifications you already have, like ISO 27001.
They might already satisfy some NIS2 requirements, saving you time and effort.
Don't overlook previous security assessments and audit findings either.
There's often valuable information buried in those reports that can inform your current analysis.
NIS2 puts specific responsibilities on the shoulders of management.
Have your executives formally approved your cybersecurity risk management measures as required by Article 20? Do you have mechanisms in place for management to oversee implementation?
Check whether your management team has received cybersecurity training.
NIS2 requires this, along with similar training for employees.
Do you have documentation showing management's involvement in cybersecurity decisions and governance? Are there regular reporting processes keeping them informed?
Make sure your leadership team understands they could be personally liable for compliance failures.
Nothing focuses the mind quite like knowing there's personal skin in the game.
Take a good look at your risk analysis policies and procedures.
Do they match what NIS2 requires?
Your information system security policies should be comprehensive and actually working in practice, not just existing on paper.
Examine how you evaluate effectiveness of your cybersecurity measures.
Is there a formal process, or is it more ad hoc?
Check if basic cyber hygiene practices are consistently applied throughout your organization – these fundamentals are often the backbone of good security.
Verify that you're using multi-factor authentication or continuous authentication solutions where appropriate.
Review your access control policies, how you handle security in HR processes, and your asset management practices.
These are all areas NIS2 specifically addresses.
When it comes to incident response, NIS2 has clear expectations.
Evaluate your incident handling procedures against these requirements.
Do you have a clearly documented process for responding to and reporting cybersecurity incidents?
Check your notification procedures for alerting Computer Security Incident Response Teams (CSIRTs) or authorities when something goes wrong.
Do you have a process for notifying service recipients if an incident might affect them?
Look at your documentation for early warnings, incident notifications, status updates, and final reports.
NIS2 requires final incident reports within one month – does your timeline align with this?
Don't forget to assess your emergency communication systems.
If an incident occurs, can people within your organization communicate securely?
Supply chain vulnerabilities have become a major attack vector, and NIS2 recognizes this reality.
How do you manage security in your relationships with suppliers and service providers? Do you assess their cybersecurity practices before signing contracts?
Look at your security measures for acquiring, developing, and maintaining systems.
Do you consider each supplier's specific vulnerabilities?
Review how you evaluate their secure development procedures and overall cybersecurity practices.
Check whether your contracts include security requirements and how you monitor suppliers' compliance with these requirements.
A chain is only as strong as its weakest link, and in cybersecurity, that weak link is often in the supply chain.
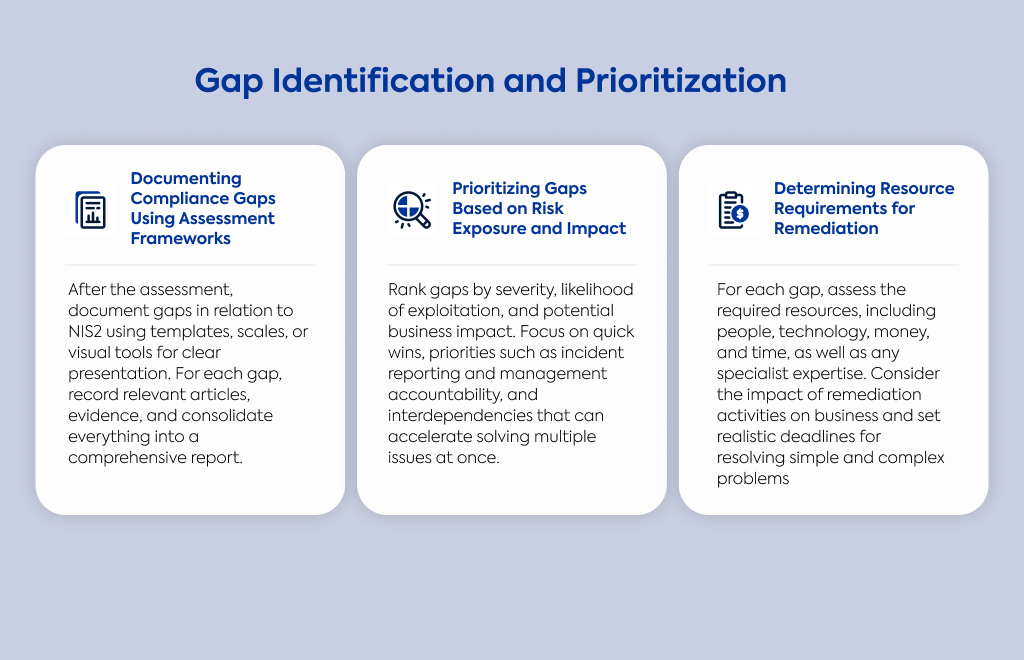
Now that you've completed your assessment, it's time to document where your current practices fall short of NIS2 requirements.
Using structured templates helps organize this information clearly.
Apply your assessment framework (like that 5-point scale mentioned earlier) to quantify each gap's severity.
Visual tools like heat maps or dashboards can help communicate the status to stakeholders who might not want to wade through detailed reports.
For each gap, note the specific NIS2 articles and paragraphs that apply.
This makes addressing the gaps more straightforward.
Document the evidence supporting your findings so you can defend your assessment if questioned.
Pull everything together into a comprehensive gap analysis report.
This gives everyone a clear picture of where you stand and what needs fixing.
Not all gaps deserve equal attention.
Some are more urgent than others, so categorize them based on severity and potential impact on your operations and compliance status.
When deciding what to tackle first, consider how likely it is that a vulnerability will be exploited and what might happen if it is.
Think about potential societal and economic impacts as mentioned in Article 21 of NIS2.
Look for "quick wins" – gaps you can address relatively quickly with minimal resources.
These early successes build momentum and show progress to stakeholders.
Gaps related to incident reporting and management responsibilities often need high priority because they directly affect compliance.
Also consider dependencies – sometimes fixing one issue helps resolve several others, making it a more efficient place to start.
For each gap, estimate what you'll need to fix it.
This means thinking about money, people, technology, and time.
Consider whether you need new roles or responsibilities to address certain gaps.
Some issues might require specialized expertise that you don't currently have in-house.
Be realistic about timelines.
Complex issues might take months to address properly, while simpler fixes could be implemented in days or weeks.
Think about how remediation activities might affect your operations.
Will fixing certain issues require downtime or changes to how people work?
These factors influence both your approach and timeline for addressing gaps.
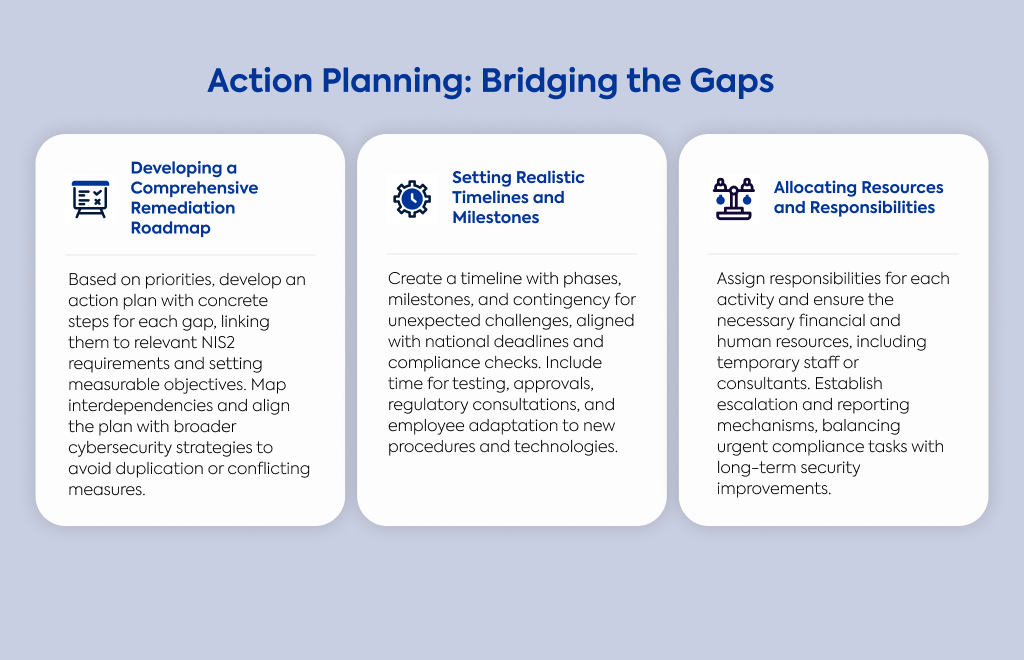
With your gaps identified and prioritized, it's time to create a detailed action plan.
Outline specific steps to address each gap, linking each action directly to the relevant NIS2 requirements.
Include clear, measurable objectives so you'll know when you've successfully resolved an issue.
Define exactly what deliverables you expect from each action item.
Map out dependencies between different actions. Some things need to happen in a particular order.
Align your roadmap with your broader cybersecurity strategy to avoid duplicating efforts or implementing contradictory measures.
Create a timeline based on your concrete national implementation deadlines and compliance checks.
Break it down into phases with intermediate milestones so you can track progress and adjust course if needed.
Give yourself enough time to test and validate implemented measures.
There's nothing worse than thinking you've fixed something only to discover it's still a problem during an audit.
Factor in time for approval processes and potential regulatory consultations – these often take longer than expected.
Consider how long organizational change management might take too.
People need time to adjust to new procedures and technologies.
Build in buffer time for unexpected challenges.
Something almost always takes longer than planned, so giving yourself some wiggle room helps ensure you meet deadlines despite surprises.
Be specific about who's responsible for each remediation activity.
Assign clear ownership to individuals or teams so there's no confusion about who's doing what.
Secure budget commitments for the investments you'll need.
Without financial resources, your action plan remains theoretical rather than practical.
Balance resources between immediate compliance needs and longer-term security improvements.
While meeting compliance deadlines is urgent, don't neglect foundational security improvements that provide lasting benefits.
Establish clear paths for escalating issues when resource conflicts or implementation challenges arise.
Define reporting requirements so responsible parties keep everyone informed throughout implementation.
Consider whether temporary staff or consultants might help with specialized tasks.
Sometimes bringing in extra hands for specific activities is more efficient than stretching your existing team too thin.
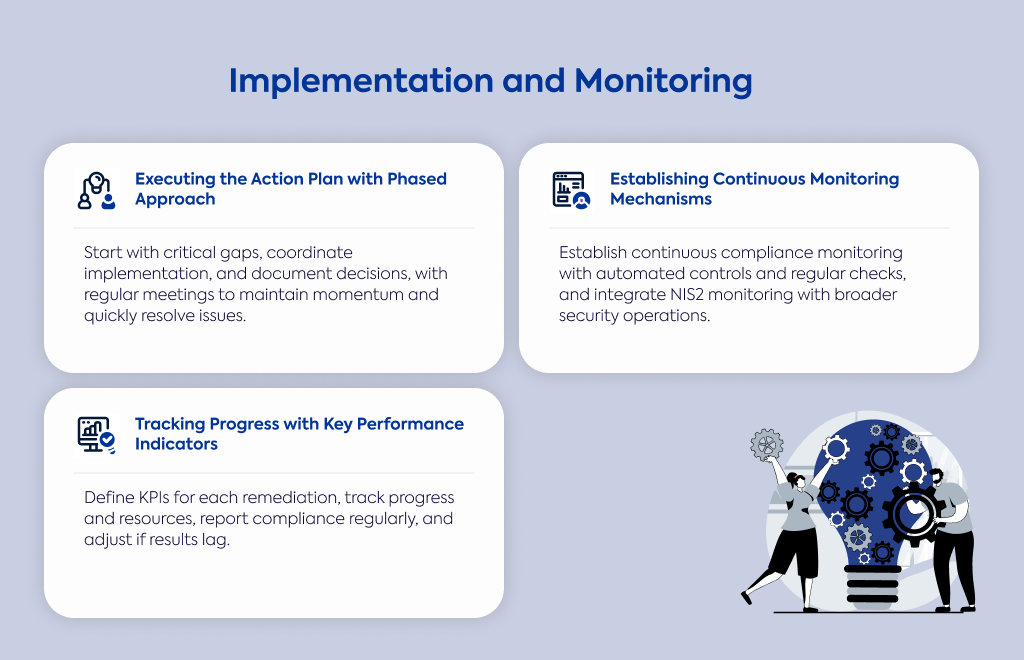
Start with your highest priority gaps to address critical compliance issues first.
Coordinate implementation across different departments to ensure consistency throughout your organization.
Follow change management procedures to minimize disruption.
Document your implementation decisions and any approved deviations from the original plan – you might need to explain these choices later.
Hold regular status meetings with the people responsible for implementation.
This helps maintain momentum and lets you address issues quickly before they derail your progress.
Once you've addressed your gaps, you need systems to ensure they stay fixed.
Develop processes for ongoing compliance monitoring after your initial implementation.
Where possible, implement automated controls and monitoring to reduce manual work.
This makes ongoing compliance more sustainable with fewer resources.
Set up triggers for compliance reassessment when systems or processes change.
New technologies or business changes can create new gaps if you're not watching for them.
Create visual dashboards showing compliance status across your organization.
This makes it easier to spot issues before they become serious problems.
Design regular verification procedures to ensure continued adherence to NIS2 requirements.
Consider integrating your NIS2 monitoring with your broader security operations monitoring.
This integration creates a more cohesive security program and reduces duplication of effort.
Establish measurable KPIs for each remediation activity and your overall compliance progress.
These give you objective ways to track how you're doing.
Create regular reporting mechanisms that show compliance status and remediation progress.
Define thresholds that trigger additional action when KPIs indicate problems.
Compare your actual progress against planned timelines and milestones.
Are you on track, or do you need to adjust your approach?
Monitor resource usage against your allocated budgets to avoid cost overruns.
Track incident response metrics to see if your new measures are actually improving your security posture.
If they're not having the expected impact, you might need to adjust your approach.
Keep all your compliance-related documentation in one central place.
This makes it much easier to find what you need during audits or regulatory reviews.
Regularly update your policies, procedures, and technical documentation to match NIS2 requirements.
Document your risk assessments, security measures, and evidence of implementation.
Maintain records showing management approval for cybersecurity risk management measures.
Create and update documentation for incident handling, business continuity, and disaster recovery as required by the directive.
Don't forget to generate evidence of staff training on cybersecurity practices.
Training records often form an important part of demonstrating compliance to auditors.
Create executive summaries that highlight key compliance status and risks.
Keep these concise but informative, focusing on what management really needs to know.
Tailor reports for different stakeholders with appropriate detail levels.
What the board needs differs from what your security team requires.
Include financial implications in your management reporting.
This helps leaders understand the business impact of cybersecurity measures and compliance status.
Show progress against your remediation roadmap, highlighting achieved milestones.
Note what resources you still need for remaining activities so management can plan accordingly.
Be transparent about potential business impacts if certain compliance gaps aren't addressed.
Leaders need to understand the risks to make informed decisions about priorities and resources.
Create audit-ready documentation packages aligned with NIS2 requirements.
When auditors arrive, you want everything they might request already organized and available.
Run internal compliance audits to find potential issues before regulatory reviews.
It's always better to discover and fix problems yourself than have auditors point them out.
Prepare key personnel for potential interviews with auditors or regulators.
Make sure they understand what might be asked and how to respond accurately.
Document all remediation activities and any deliberate risk acceptance decisions.
If you've chosen not to address certain gaps, you need to explain your reasoning.
Maintain evidence of your continuous monitoring and improvement efforts.
This shows auditors you're actively managing compliance, not just reacting to problems.
Have a process ready for addressing and documenting any findings that come up during audits or regulatory reviews.
Knowing in advance how you'll handle issues helps you respond more effectively.

Instructions: Answer each question by selecting the option that best represents your organization's current implementation status.
This assessment will help determine your NIS2 compliance readiness level.
Implementation Status Options:
Not Implemented: No processes or controls exist, or they are in early planning stages
Partially Implemented: Processes or controls exist but are not fully operational or documented
Fully Implemented: Processes or controls are completely implemented, documented and regularly reviewed
Management Responsibility and Governance
Has your management body formally approved cybersecurity risk management measures?
Not Implemented
Partially Implemented
Fully Implemented
Does your management body actively oversee the implementation of cybersecurity risk management measures?
Not Implemented
Partially Implemented
Fully Implemented
Have management body members completed cybersecurity training, and are similar training programs available to employees?
Not Implemented
Partially Implemented
Fully Implemented
Risk Management Framework
Has your organization implemented proportionate technical, operational, and organizational measures to manage cybersecurity risks?
Not Implemented
Partially Implemented
Fully Implemented
Do you have documented policies for risk analysis and assessment?
Not Implemented
Partially Implemented
Fully Implemented
Do you have formal policies for information system security?
Not Implemented
Partially Implemented
Fully Implemented
Does your organization have a process to evaluate the effectiveness of cybersecurity measures?
Not Implemented
Partially Implemented
Fully Implemented
Incident Management
Do you have documented procedures for cybersecurity incident handling?
Not Implemented
Partially Implemented
Fully Implemented
Do you have established protocols for notifying relevant authorities of significant cybersecurity incidents?
Not Implemented
Partially Implemented
Fully Implemented
Does your organization have procedures to notify service recipients of incidents that may affect them?
Not Implemented
Partially Implemented
Fully Implemented
Business Continuity and Recovery
Do you have documented business continuity plans addressing cybersecurity incidents?
Not Implemented
Partially Implemented
Fully Implemented
Has your organization implemented backup management procedures?
Not Implemented
Partially Implemented
Fully Implemented
Do you have documented disaster recovery and crisis management plans?
Not Implemented
Partially Implemented
Fully Implemented
Supply Chain Security
Do you have procedures to assess and manage security risks from suppliers and service providers?
Not Implemented
Partially Implemented
Fully Implemented
Do you conduct security assessments of key suppliers' cybersecurity practices?
Not Implemented
Partially Implemented
Fully Implemented
Technical Security Controls
Has your organization implemented basic cyber hygiene practices across all systems?
Not Implemented
Partially Implemented
Fully Implemented
Do you use multi-factor authentication or continuous authentication solutions?
Not Implemented
Partially Implemented
Fully Implemented
Have you implemented encryption and secure communications for sensitive data?
Not Implemented
Partially Implemented
Fully Implemented
Do you have formal access control policies and asset management procedures?
Not Implemented
Partially Implemented
Fully Implemented
Do you have secure emergency communication systems within your organization?
Not Implemented
Partially Implemented
Fully Implemented
Scoring Method:
Not Implemented = 0 points
Partially Implemented = 1 point
Fully Implemented = 2 points
Total possible score: 40 points
Level | Score Range | Readiness Status | Description |
1 | 0-8 | Early Planning | Your organization is in the early stages of NIS2 compliance. Significant work is needed across all areas to meet the directive's requirements. Immediate action is required to establish basic cybersecurity governance and controls before compliance checks begin in 2026. |
2 | 9-16 | Foundation Building | Basic cybersecurity elements are in place, but substantial gaps remain in governance, risk management, and technical controls. Focus on developing formal policies and establishing management oversight to advance compliance efforts. |
3 | 17-24 | Developing Compliance | Your organization has implemented many required elements but lacks full documentation or complete implementation. Prioritize incomplete areas and establish monitoring mechanisms to track progress toward full compliance. |
4 | 25-32 | Advanced Implementation | Most NIS2 requirements are in place with proper documentation. Focus on optimizing existing controls, conducting regular assessments, and ensuring consistent application across the organization. |
5 | 33-40 | Optimized Compliance | Your organization demonstrates comprehensive NIS2 compliance with full implementation of required controls. Maintain this status through continuous improvement, regular testing, and adapting to evolving threats and regulatory changes. |
Note: This assessment provides a high-level view of your NIS2 compliance readiness, not a definitive compliance determination. Even high scores (33-40) indicate strong preparation but don't guarantee full regulatory compliance. The questionnaire covers key areas but isn't exhaustive, and doesn't measure implementation quality. Organizations should conduct a detailed gap analysis of all NIS2 requirements and maintain ongoing monitoring processes. True compliance is ultimately determined by regulatory authorities.
Feeling overwhelmed by the complexity of NIS2 compliance? You're not alone.
The detailed gap analysis process, technical requirements, and looming 2026 compliance checks can be daunting – especially with the potential for hefty fines and personal liability for management.
Why navigate these challenges by yourself when Gauss can help?
Our specialized NIS2 compliance service takes the guesswork out of the process.
We'll guide you through each step of the gap analysis, help prioritize your remediation efforts, and ensure your documentation meets regulatory standards.
Our team of cybersecurity experts understands both the technical and regulatory aspects of NIS2, allowing you to focus on what you do best – running your business.
Contact us today to discuss how we can simplify your path to NIS2 compliance.